- Home
- Services
- Testing & Qualification
- Mechatronic Systems Compliance
- Cyber Resilience Act
- Home
- Services
- Testing & Qualification
- Mechatronic Systems Compliance
- Cyber Resilience Act
Cybersecurity across the lifecycle
What the CRA is really about
Understanding and implementing requirements for products with digital elements.
The Cyber Resilience Act (CRA) establishes, for the first time, a harmonised, EU-wide framework for the cybersecurity of connected products with digital elements. This includes not only traditional IT products, but also networked machinery, control systems and software-based components.
Unlike previous regulations, the CRA does not focus solely on placing products on the market. It addresses the entire lifecycle — from development and operation through to end-of-life.
For manufacturers, this means that cybersecurity becomes an end-to-end responsibility — spanning technical, organisational and regulatory domains.
What you should know about the CRA - FAQ
Which products are affected?
The CRA applies to products with digital elements that are made available on the market and whose intended or reasonably forseeable use includes a direct or indirect communication interface with other devices or networks.
This applies in particular to
- products with remote access or update capabilities
- software integrated into mechatronic systems
- software with communication interfaces
Important: The requirements apply not only to new products, but also to existing products with digital elements and communication interfaces that continue to be made available on the market after the CRA enters into force.
Key roles and responsibilities
The CRA distinguishes between different actors along the value chain. Depending on the role, different obligations apply:
- manufacturers (development and placing on the market)
- importers (introduction into the EU market)
- distributors (making products available on the market)
- authorised representatives (representation of the manufacturer within the EU)
- persons responsible for open-source components
For companies, it is therefore crucial to clearly determine their own role − and to derive the corresponding requirements from it.
What does the CRA require in practice?
Requirements along the product life cycle
The requirements of the CRA are not limited to a single point in time; they are structured across the entire product lifecycle.
Development and design
Cybersecurity requirements must be systematically considered during the development phase:
- security by design and secure by default
- structured risk management
- integration of trustworthy software components
- avoidance of known vulnerabilities
Cybersecurity thus becomes an integral part of the system architecture.
Conformity and placing on the market
Before a product can be placed on the market, manufacturers must demonstrate that it meets the requirements:
- technical documentation
- security and functional testing
- conformity assessment procedures
- CE marking and EU declaration of conformity
This evidence must be consistent and comprehensively documented
Operation
A key difference compared to previous regulatory frameworks lies in the responsibilities during the usage phase:
- provision of security updates
- structured vulnerability management
- reporting obligations for actively exploited vulnerabilities and serious security incidents
- provision of security-relevant information
Manufacturers therefore remain responsible even after the product has been placed on the market.
End of life
The end of the product lifecycle is also explicitly addressed:
- clear indication of the end of support (end of life) and resulting limitations
- transparent communication of residual risks
- defined handling of unsupported systems
From this point onwards, responsibility for secure operation lies with the user.
In cases involving software integration: if support for integrated third-party software expires, responsibility shifts to the integrator.
Why implementing the CRA is complex
The challenge does not lie in individual requirements, but in how they interact. In practice, several factors make implementation demanding:
- cybersecurity must be integrated into existing development processes
- requirements overlap with the Machinery Regulation and the AI Act
- responsibility extends over the entire lifecycle
- organisational structures must be adapted
The alignment between development, IT, security and compliance is particularly challenging.
When does the CRA come into force?
The EU Cyber Resilience Act (CRA) regulation will come into full force from December 11, 2027.
However, parts of it will apply earlier.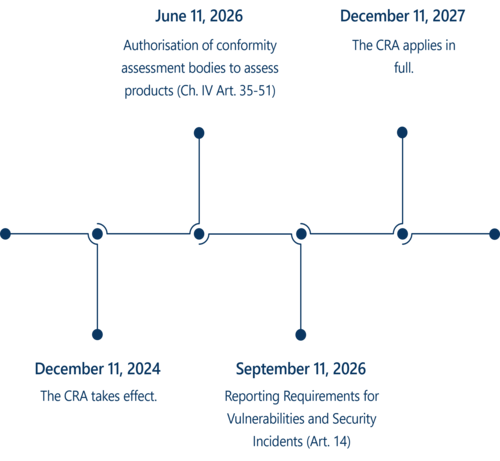
What happens in the event of non-compliance?
Infringement Consequences Non-compliance with essential cybersecurity requirements Fines of up to €15 million or 2.5% of total worldwide annual turnover in the preceding financial year, whichever is higher Breach of other obligations, such as documentation and conformity assessment procedures Fines of up to €10 million or 2% of total worldwide annual turnover in the preceding financial year, whichever is higher False, misleading or incomplete information provided to notified bodies or market surveillance authorities Fines of up to €5 million or 1% of total worldwide annual turnover in the preceding financial year, whichever is higher Important: For newly established companies and SMEs, the lower amount applies instead of the higher one.
If identified non-compliance with the requirements of the Cyber Resilience Act is not remedied within the specified timeframe following a request by the market surveillance authority, this may have direct implications for your ability to place the product on the market.
In practice, this can range from restrictions on the continued availability of the product to a complete suspension of sales. In serious cases, a recall of products already placed on the market may also be required.
Early and structured implementation of the requirements helps to avoid such risks and to ensure the continuous availability of your products on the market.
Why this matters to you
The new European regulations do not only affect individual departments. They have an impact across product development, IT, quality management, procurement and executive management alike. For manufacturers of mechatronic systems, the following implications are particularly significant:
Increased requirements for development processes
Security and AI aspects must be considered and documented at an early stage.Extended responsibility during operation
With the Cyber Resilience Act, the focus expands significantly into the usage phase. Vulnerability management, updates and monitoring become ongoing responsibilities.Rising complexity in compliance and documentation
Overlapping requirements from multiple regulations require a consistent documentation strategy.Need for organisational adaptation
Roles, responsibilities and interfaces must be clearly defined − particularly for software and AI components.
For many companies, the key challenge lies in bringing these requirements together in a structured way. A systematic approach creates transparency, reduces liability risks and increases planning security when introducing complex systems to the market.
Structured implementation with IABG experts
The requirements of the Cyber Resilience Act cannot be considered in isolation. They affect existing processes, systems and organisational structures.
We support you in implementing them in a structured way – from assessing applicability and integrating requirements into development processes through to ensuring secure operation.
Get more information:
Safeguarding of mechatronic systems
Cyber security
AI Assurance & safeAI
I am looking forward to your message.

How can we help you?
Please fill in the form and we will get in touch with you as soon as possible.
This section contains third-party content that you can view with a single click.
By loading the form, personal data may be transmitted to the third-party provider. You can find more information in our privacy policy
